OE Federal Credit Union
oefederal.orgDescription:
DNS Records:
The following DNS records were found for the victim's domain.
- abusegodaddy.com
- mail.oefederal.org.
- mx1.hc2790-20.iphmx.com. Cisco/IronPort
- mx2.hc2790-20.iphmx.com. Cisco/IronPort
- google-site-verification=RQInhl_8ILbQfzTl3mJ5PHzLOtVgIxGZ3exCuafrx8E
- facebook-domain-verification=coczr101bmgv5rxjiytbmilw4zpequ
- nbltbd0rq564alr4b5gfut4o82
- knowbe4-site-verification=46d05c31a6528247f958518124dd0363
- v=spf1 ip4:216.71.148.87 ip4:63.117.120.96/27 ip4:131.239.15.160/27 ip4:208.252.57.192/27 ip4:149.20.203.80 ip4:208.235.248.20 ip4:45.62.187.42" " ip4:149.72.182.202 ip4:149.72.224.42 ip4:149.72.249.133 ip4:149.72.24.125 ip4:149.72.24.148 ip4:50.31.35.233 ip4:149.72.32.86 ip4:149.72.32.64 ip4:149.72.32.11" " ip4:149.72.31.26 ip4:149.72.30.233 ip4:149.72.30.217 ip4:149.72.28.49 ip4:149.72.28.198 ip4:149.72.238.186 ip4:149.72.84.85 ip4:149.72.56.59 ip4:167.89.91.252" " ip4:205.220.177.135 ip4:205.220.166.201 ip4:52.128.103.21 ip4:52.128.103.23 ip4:52.128.103.24 ip4:66.159.240.191 ip4:66.159.238.164 ip4:52.100.0.0/15 ip4:52.102.0.0/16 ip4:52.103.0.0/17" " ip4:40.92.0.0/15 ip4:40.107.0.0/16 ip4:104.47.0.0/17 ip6:2a01:111:f400::/48 ip6:2a01:111:f403::/49 ip6:2a01:111:f403:8000::/51 ip6:2a01:111:f403:c000::/51 ip6:2a01:111:f403:f000::/52" " ip4:216.116.80.0/24 ip4:216.116.81.88 ip4:216.116.87.0/24 ip4:74.200.60.0/24 ip4:74.200.63.0/24 ip4:216.116.95.0/24 ip4:52.128.98.34 ip4:52.128.98.35 ip4:52.128.98.36" " ip4:149.72.122.140 ip4:149.72.122.84 ip4:149.72.113.109 ip4:149.72.113.11 ip4:149.72.116.97 ip4:149.72.120.226 ip4:149.72.123.170 ip4:149.72.123.174 ip4:149.72.47.228" " ip4:149.72.126.151 ip4:149.72.43.169 ip4:167.89.18.202 ip4:167.89.45.114 ip4:168.245.109.51 ip4:168.245.34.52 ip4:168.245.50.27 ip4:168.245.51.175 ip4:192.254.113.110 ip4:166.73.7.20 ip4:153.69.200.104 ip4:153.69.195.103" " ip4:209.61.151.0/24 ip4:166.78.68.0/22 ip4:198.61.254.0/23 ip4:192.237.158.0/23 ip4:23.253.182.0/23 ip4:104.130.96.0/28 ip4:146.20.113.0/24 ip4:146.20.191.0/24 ip4:159.135.224.0/20 ip4:69.72.32.0/20 ip4:104.130.122.0/23 ip4:146.20.112.0/26" " ip4:161.38.192.0/20 ip4:143.55.224.0/21 ip4:143.55.232.0/22 ip4:159.112.240.0/20 ip4:198.244.48.0/20 ip4:204.220.168.0/21 ip4:204.220.176.0/20 ip4:216.71.143.51" " a mx mx:res.cisco.com exists:%{i}.spf.res.cisco.com include:cust-spf.exacttarget.com include:docebosaas.com include:amazonses.com include:spf.webaccess1.com include:_spf.eu.mailgun.org include:gateways.firstdata.com ~all
- smartsheet-site-validation=PZdkynIpUvlaCDkqNr3MCmz0TduDKRFE
- apple-domain-verification=zI7nXGctOrnL96tD
- MS=ms52624655
Cloud / SaaS Services Detected
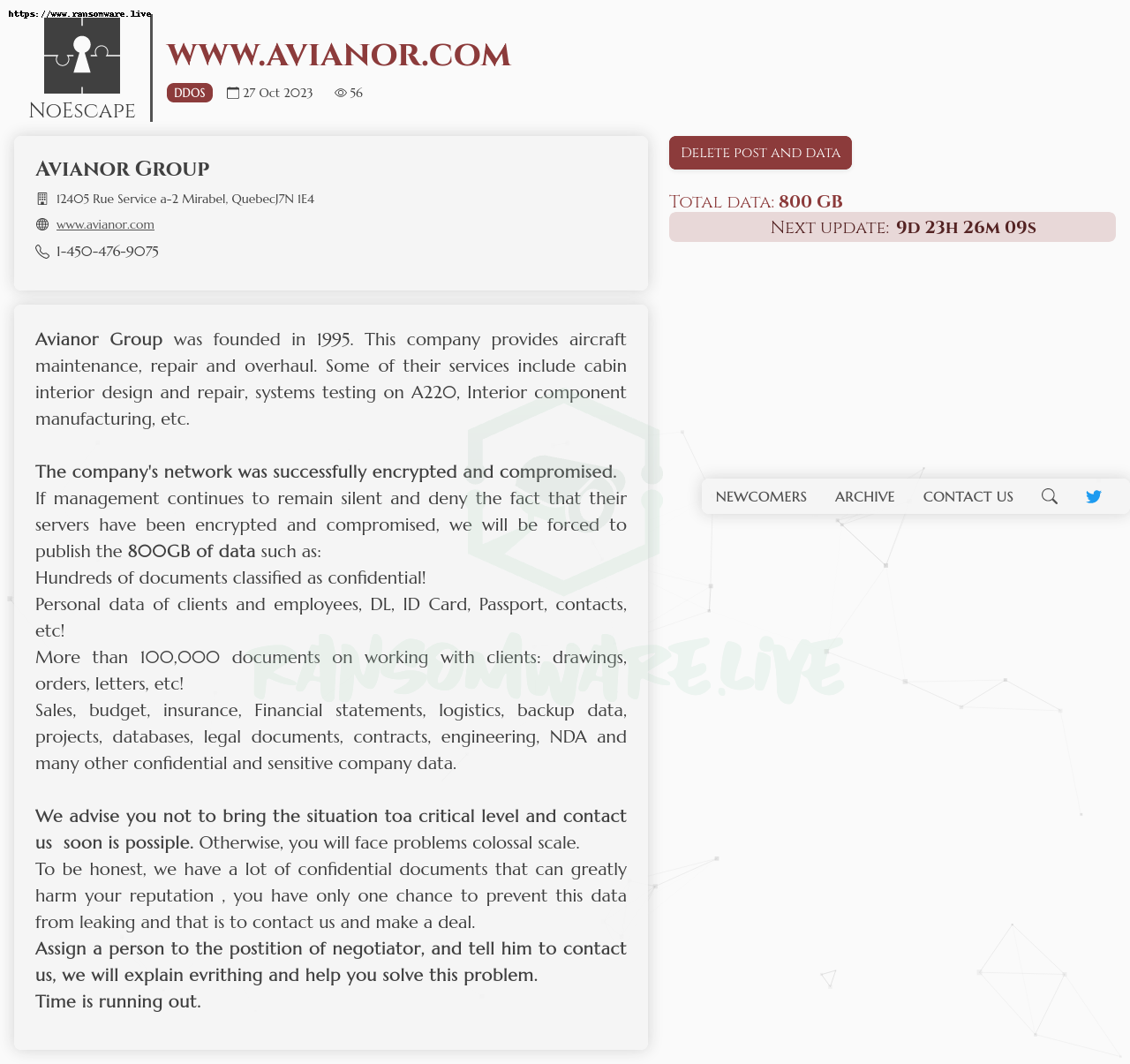
Leak Screenshot:
Legal Disclaimer: Ransomware.live does not engage in the acquisition, exfiltration, downloading, possession, hosting, access, consultation, redistribution, or disclosure of unlawfully obtained data. This platform indexes only publicly visible information posted by ransomware operators and open web sources without accessing or obtaining the underlying stolen content. The service is provided to support public awareness, legitimate research, and cyber-resilience. No stolen personal or confidential data is collected or distributed via this site.
